Website security encompasses all the methods and practices aimed at protecting websites from cyberattacks and data breaches. This article explains the 10 ways to secure a website. We’ll explain the most relevant threats to websites, how to make sense of global web security standards and which security tools are recommended.
We also explain effective website security strategies such as choosing secure hosting, installing firewalls and SSL certificates, utilizing Content Delivery Networks (CDNs), and malware scanning.

What is Website Security?
Website security refers to the measures and protocols designed to protect a website from malicious attacks. Worldwide cybercrime damages are estimated to reach $10.5 trillion annually according to Cybersecurity Ventures. These immense potential losses underscore the growing need for strong website security protocols across all websites.
What is the importance of website security?
The importance of website security is that it protects data, prevents attacks, ensures compliance, and improves visibility. Protecting website and user data keeps sensitive information safe from unauthorized access. Preventing malware and attacks safeguards the website’s functionality and integrity. Compliance with regulations such as GDPR, CCPA, and HIPAA avoids legal penalties and builds visitor trust. Finally, secure websites are favored by search engines and get higher rankings.
What are the signs of compromised website security?
There are 6 signs of compromised website security:
- Unexpected redirects Unexpected redirects often indicate that malicious scripts are directing visitors to unintended destinations.
- Unwanted ads and popups Unwanted adverts and pop-ups appearing on your website suggest adware has been injected into your site.
- High or spiking CPU usage High or spiking CPU usage on the server is a possible sign of a malware infection or ongoing attack using excessive resources.
- New web pages containing spam keywords being indexed< New pages containing spam keywords typically mean your site has been compromised to spread spam or phishing attacks.
- Unexpected JavaScript Unexpected JavaScript on the website sometimes indicate that attackers have manipulated your site to execute malicious scripts on users’ browsers.
- Browser warnings Browser warnings when visiting the website usually signal that the site is recognized as harmful, often due to malware.
What are the 10 ways to secure a website?
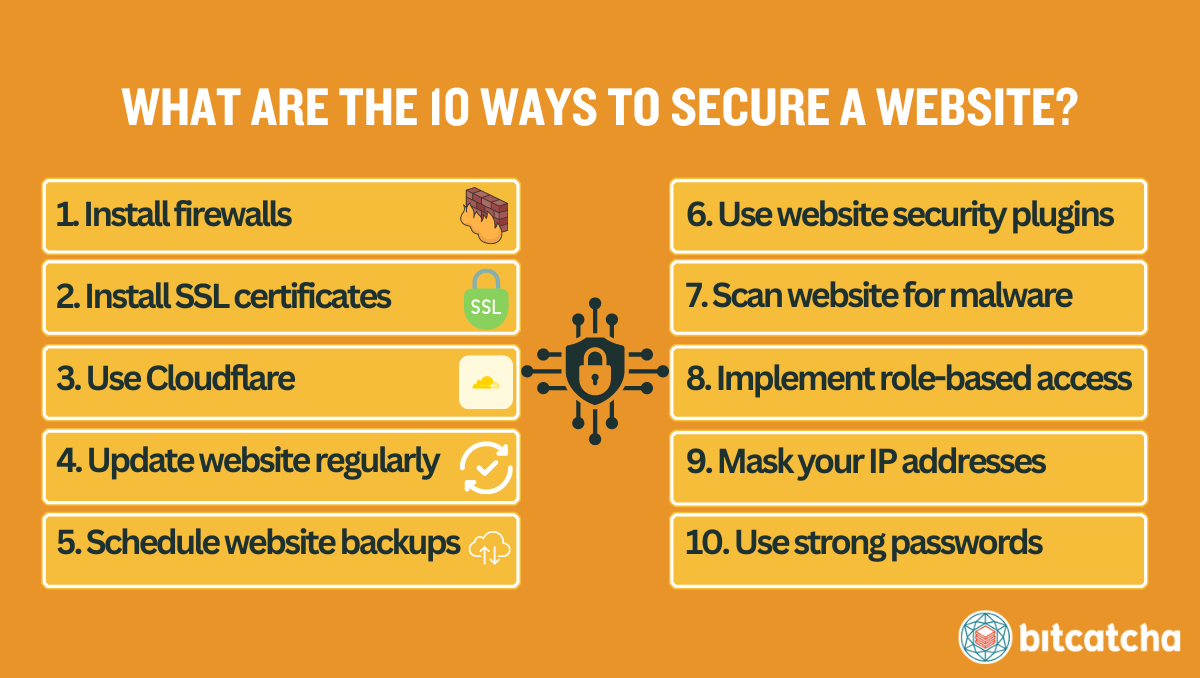
There are 10 ways to secure a website:
- Install firewalls
- Install SSL certificates
- Use Cloudflare
- Update website regularly
- Schedule regular website backups
- Use website security plugins
- Scan website for malware regularly
- Implement role-based access control
- Mask your IP addresses
- Use strong passwords
1. Install firewalls
Install firewalls as the foundational step to securing your website. A firewall is a barrier between your website and external threats and filters out unwanted traffic and potential breaches. There are 2 essential types of firewalls: network firewalls and web application firewalls (WAFs). A network firewall secures the perimeter of your network by managing access by blocking or permitting traffic based on predetermined security rules. A WAF protects by filtering and monitoring HTTP traffic between an application and the Internet.
Take action by verifying through your web hosting control panel that a network firewall is active. Also implement a WAF either through a CDN or through specific security plugins.
2. Install SSL certificates
Install SSL certificates, to protect sensitive data being transmitted between your website and its users. A SSL (Secure Sockets Layer) certificate is a digital certificate that uses the SSL/TLS encryption protocol to create a secure connection that secures transmitted data like usernames, passwords, and credit card information.
Take action by installing SSL certificates from trusted certificate authorities (CA) like Cloudflare, Let’s Encrypt, ZeroSSL, or SSL For Free. Many web hosting providers and website builders offer free SSL certificates in their plan. Ensure that SSL protection extends across all pages of your website so that every web page is served on HTTPS.
3. Use Cloudflare
Use Cloudflare to enhance your website security. Cloudflare is a reverse proxy that sits in between your server and the internet. It helps to monitor your website traffic. Cloudflare is able to mitigate DDoS attacks, provides a Web Application Firewall (WAF), and supports SSL/TLS encryption, thus adding an additional layer of security. Cloudflare also speeds up the loading time of your website.
Take action by setting up Cloudflare for your website.
4. Update website regularly
Update your website regularly by actively keeping your website components up-to-date with their most recent versions. Website updates often include security patches that address potential vulnerabilities and new cyberthreats. Updates also improve the overall performance and functionality of your site. There are 5 website components to keep updated: CMS, themes, plugins, third-party APIs, and its database management system.
Take action by first disabling automatic updates. Automatic updates often cause compatibility issues. Test all website updates on a staging server first, instead. If the update is proved successful on the staging site, then apply them to the production server.
5. Schedule regular website backups
Schedule regular backups to recover your website quickly and efficiently after data loss or a cyberattack. A website backup is the process of copying and storing website data (website files, databases, emails) that are easily restored in case of data loss.
Take action by implementing a backup schedule that includes daily, weekly and monthly backups. Ensure you make additional backups before major website changes. Use tools available in your web hosting control panel, CMS, or manual methods such as FTP/SFTP.
6. Use website security plugins
Use website security plugins to secure your website thoroughly. Website security plugins provide a robust suite of tools designed to enhance your website’s security. These plugins monitor website activity, scan for malware, implement security hardening measures, and protect against brute force attacks. There are also plugins that specialize in ensuring compliance with cybersecurity standards such as PCI DSS, GDPR, CCPA, HIPAA.
Take action by installing the security plugins that best fit your needs. Popular options include Wordfence, All in One WP Security, and Sucuri.
7. Scan website for malware regularly
Scan your website for malware regularly to detect and remove harmful software before it affects your website’s functionality and security. Malware refers to malicious software designed to exploit your website and steal sensitive data.
Take action by installing Sucuri. Sucuri is a cybersecurity suite offering excellent website security solutions like malware removal. Use Sucuri to conduct malware scans ideally on a daily basis or at least on a weekly basis. Another alternative is to seek and use a web hosting service that includes malware scanning and removal as part of its package.
8. Implement role-based access control
Implement role-based access control to prevent misuse. Role-based access control (RBAC) is a method to restrict system access to authorized users based on their roles. Implementing RBAC minimizes security breaches by ensuring individuals only have access to the information and functionality necessary for their roles.
Take action by regularly scrutinizing and adjusting user roles and permissions. Remove or downgrade access for users who do not need administrative capabilities, including inactive or superuser accounts.
9. Mask your IP addresses
Mask your IP addresses whenever you access your website to protect your login credentials. IP masking is important for webmasters because it reduces the risk of attackers successfully conducting phishing attacks to obtain your website logins and then hacking into your website. Phishing attacks are when cybercriminals impersonate legitimate entities to deceive individuals into providing sensitive information like website usernames and passwords.
Take action by using a VPN to mask your IP address whenever you access your website. A VPN is a security tool that secures your connection by establishing an encrypted connection to a VPN server, thus hiding your IP and maintaining your anonymity. This prevents tracking and reduces the risk of targeted cyber attacks to extract your website credentials.
10. Use strong passwords
Use strong passwords to protect your website from unauthorized access from malicious actors and brute force attacks. A strong password includes a mix of letters, numbers, and symbols and is unique to each account. Ensure that all administrative accounts related to your website use strong and unique passwords.
Take action by implementing multi-factor authentication (MFA) to add an extra layer of security. MFA makes it more challenging for attackers to gain unauthorized access because it requires multiple forms of verification.
What are the common website security threats?
Common website security threats disrupt or compromise website integrity and functionality by exploiting vulnerabilities. The 5 common website security threats are DDoS (distributed denial-of-service) attacks, SQL injections, XSS (Cross-Site Scripting) attacks, unauthorized hotlinking, and brute force attacks. Read our article on common web attacks to understand their individual differences.
What can I do if my website security is compromised?
If your website security is compromised you can act quickly to mitigate damage. Start by identifying the signs of compromise. Use tools like Google’s Safe Browsing and security plugins to identify defacements, unknown user accounts, or altered files, using tools. Monitor server logs for unusual activity to identify the breach source.
Once confirmed, remove suspicious accounts, change passwords, scan for malware with tools like Sucuri and update software and plugins. Restore your website from a clean backup if possible.
What are the website security standards and acts I should be aware of?
Website security standards are protocols that ensure website integrity and data protection. They include the OWASP Top Ten for web threats, the NIST Cybersecurity Framework for risk mitigation, and PCI DSS for credit card security.
Website security acts are laws that protect personal and sensitive information online. Key examples are GDPR in Europe, CCPA in the US, and HIPAA for medical information. Check our guide to learn what you need to know about these website security standards.
What are the must-have tools for securing a website?
There are 8 must-have tools for securing a website. These are secure web hosting plans, ICANN-accredited domain registrars, SSL certificates, CDNs, security plugins, cloud storage for backups, VPNs, and password managers.
What types of hosting provide strong website security?
Types of hosting that provide strong website security are VPS (Virtual Private Server) and managed web hosting services. VPS hosting isolates your environment from other users and reduces cross-site contamination risks. Managed hosting includes active security management by providers such as automatic software updates and firewall configurations that provide maximum security.
Opt for reputable web host providers that not only provide these 2 types of hosting but also throw in security features like SSL certificates, malware scanners, automated backups, and CDN integration.
How do I know if a domain registrar is ICANN-accredited?
To know if a domain registrar is ICANN-accredited, check that the registrar is on the ICANN’s List of Accredited Registrars. Cloudflare, Namecheap, GoDaddy, and Porkbun are examples of notable ICANN-accredited registrars.
Do SSL certificate types affect website security?
No, the type of SSL certificate does not affect website security. Whether the SSL is domain validated (DV), organization validated (OV), or extended validation (EV) does not impact the encryption strength. The key differences between SSL types lie in the level of validation provided about the holder’s identity, not in how they impact website security.
Can Cloudflare protect my website from DDoS attacks?
Yes, Cloudflare can protect your website from DDoS attacks by distributing traffic across various servers and thus mitigating the impact of traffic surges. They also protect you by implementing Web Application Firewalls (WAFs) that filter malicious traffic.
How do I secure my WordPress website?
To secure your WordPress website, install WordPress security plugins that provide malware scanning and firewall protection. Also keep your WordPress themes and plugins up-to-date and check you’re using the latest PHP version. Refer to our WordPress security best practices when you’re securing your site.
What is the 3-2-1 backup rule about?
The 3-2-1 backup rule is about maintaining three copies of your data on two different storage media, with one copy stored off-site. This strategy ensures data safety and accessibility in case of physical or technical problems. It’s best to use reputable cloud storage for the off-site copy.
Can using a VPN prevent identity theft?
Yes, a VPN (Virtual Private Network) can help prevent identity theft by encrypting your internet connection. A VPN service safeguards your personal information from identity thieves, especially on unsecured networks.
How do I create strong passwords?
To create strong passwords, incorporate a complex mix of uppercase and lowercase letters, numbers, and symbols to form sequences that are hard to guess. Use a leading password manager with a password generator to create and securely store these passwords.



